McAfee researchers have discovered various Google Chrome extensions. That steals browsing activity, with these add-ons recording more than a million downloads. As reported by Bleeping Computer, threat analysts from the digital security company have come across a total of five such malicious extensions.
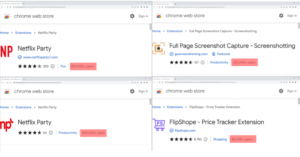
With over 1.4 million downloads, of these Chrome extensions’ 1.4 million users have tricked an unprecedented number of individuals into adding them to their browsers. The following extensions have been tracked so far:
- Netflix Party: 0.8M downloads
- Netflix Party 2: 0.3M downloads
- Full Page Screenshot: 0.2M downloads
- FlipShope — Price Tracker Extension: 80K downloads
- AutoBuy Flash Sales: 20K downloads
Can Chrome extensions steal your information?
If yes, how do they do that?
Once one of the above extensions is installed on the Chrome browser, it can subsequently detect and track when a user opens an e-commerce website in their browser. The cookie that the visitor generates is modified to appear to have arrived at the page via a referrer link. Ultimately, whoever is behind the extensions can receive an affiliate fee if the target makes a purchase from the site.
All extensions actually provide whatever functionality is listed on their Chrome Web Store pages. Coupled with the fact that they showcase a user base in the tens or hundreds of thousands, it can convince many that they are safe to download if so many individuals are using them.
While the Netflix Party extension has been removed, screenshots and price tracking are still available in the Chrome Web Store. As for how the extensions work, McAfee detailed how the web application’s manifest—the element that controls how add-ons run in the browser—runs a multipurpose script that allows it to send browsing data directly to attackers through a certain domain they have. I am registered.
Malicious Tracking Activity
When a user visits a new URL, their browsing data is sent using POST requests. This information includes the website address itself (in base64 form), the user ID, and the device location (country, city, and zip code). And the encoded referral URL. To avoid detection, some extensions do not activate their malicious tracking activity for 15 days after being installed by a target. Similarly, we’ve recently seen threat actors delay loading malware onto a system for up to a month.
Hackers have increasingly relied on hiding malicious code and malware in free Windows software and downloads. Recently, they have been targeting users with space images and also trying to hack systems through Windows Calculator. That’s all for the current Google News.
